Cybersecurity as a Service
What Is CAAS?
- Firewalls and network security
- Monitoring for attacks
- Cloud app protection (Microsoft 365, Google, Saas)
- Data protection (stop leaks)
- Security alerts & incident response
- Regular patching & updates
SASE & Government Requirement
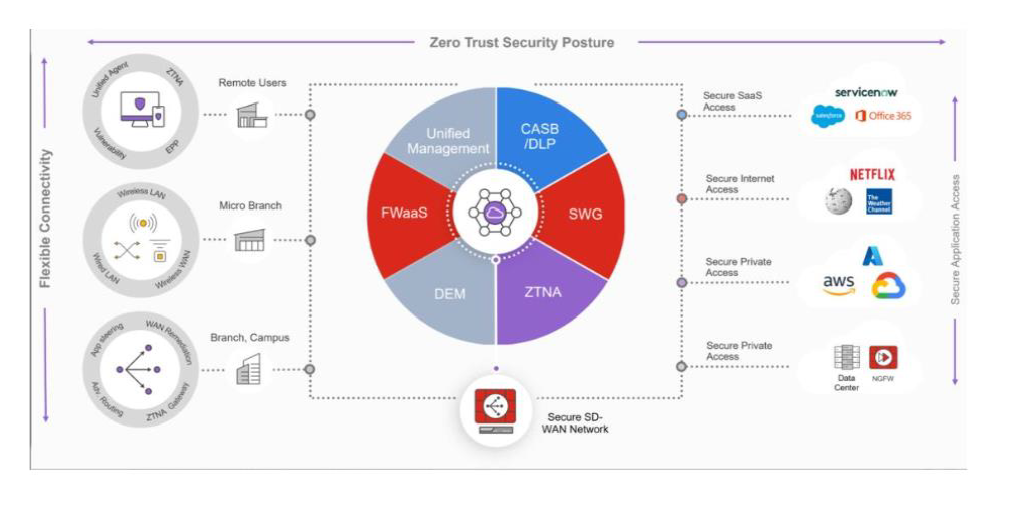
Secure Access Service Edge (SASE) significantly aids in meeting the requirements of the SOCI Act and CIST by integrating security and networking into a unified framework.
Enhanced Security
Combines ZTNA, SWG, and CASB to ensure only authenticated users access critical infrastructure, directly aligning with SOCI Act requirements.
Compliance & Monitoring
Includes robust tools for detailed logging and reporting, essential for adhering to regulatory standards and meeting CIST requirements.
Scalability & Flexibility
Adapts to the changing needs of critical infrastructure, maintaining security across diverse and evolving global environments.
Unified Management
Simplifies oversight by integrating security and networking into one platform, reducing the complexity of regulatory compliance.
A comprehensive approach to securing critical infrastructure while enhancing your overall cybersecurity posture.
Summary of Key Focus Areas & What They Mean for You
Expect higher mandatory standards.
Ensure that your service providers comply with new regulatory obligations.
Expect increased preference for Aussie or allied vendors across cloud, SaaS, and network platforms.
Emphasise threat-intel integration, rapid detection, and automated response in your architecture.
When deploying SD-WAN, Versa, Omada, or UDM, factor in supply-chain risk and device hardening as default.
Ensure your cyber posture meets global standards and aligns with partner nations’ expectations.

Why Businesses Need CAAS
Combining networking (SD-WAN) and security into one unified, cloud-delivered platform.
Users Work Everywhere Now
- Staff no longer sit in one office connected to a firewall.
- Employees now work remotely.
- Branches are smaller and distributed.
- Devices connect from home networks, 4G, and public Wi-Fi.
- Most business applications are now cloud-based.
Security Needs to Be Everywhere
Old security model: One large firewall at headquarters.
Modern threats and cloud applications require security that isn’t in one box, but integrated into the fabric of the network.
- Identity-driven access
- Global policy enforcement
- Real-time threat mitigation
The essential components of a robust SASE architecture